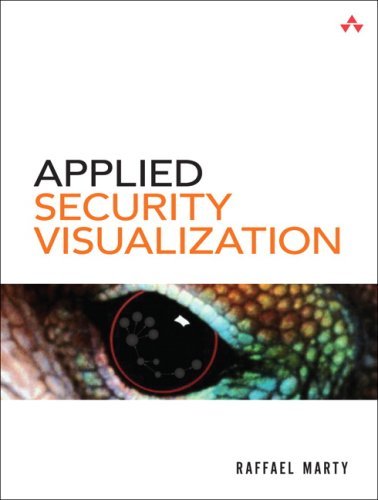
 Author: Raffael Marty
Author: Raffael Marty
Publisher: Addison Wesley Professional
ISBN-10: 0-321-51010-0
ISBN-13: 978-0-321-51010-5
Pages: 552
Publisher Book Home: http://www.informit.com/store/product.aspx?isbn=0321510100
Safari (electronic version): http://safari.informit.com/9780321585530
Marketing Material: Book Flyer
Sample Chapter: Download Chapter 5
Video Interview: Interview with Raffael Marty.
Latest version of DAVIX: http://82.197.185.121/davix/release/davix-latest.iso.gz
“Collecting log data is one thing, having relevant information is something else. The art to transform all kinds of log data into meaningful security information is the core of this book. Raffy illustrates in a straight forward way, and with hands-on examples, how such a challenge can be mastered. Let's get inspired.”
–Andreas Wuchner, Head of Global IT Security, Novartis
Use Visualization to Secure Your Network Against the Toughest, Best-Hidden Threats
As networks become ever more complex, securing them becomes more and more difficult. The solution is visualization. Using today’s state-of-the-art data visualization techniques, you can gain a far deeper understanding of what’s happening on your network right now. You can uncover hidden patterns of data, identify emerging vulnerabilities and attacks, and respond decisively with countermeasures that are far more likely to succeed than conventional methods.
In Applied Security Visualization, leading network security visualization expert Raffael Marty introduces all the concepts, techniques, and tools you need to use visualization on your network. You’ll learn how to identify and utilize the right data sources, then transform your data into visuals that reveal what you really need to know. Next, Marty shows how to use visualization to perform broad network security analyses, assess specific threats, and even improve business compliance.
He concludes with an introduction to a broad set of visualization tools. The book’s CD also includes DAVIX, a compilation of freely available tools for security visualization.
You'll learn how to:
- Intimately understand the data sources that are essential for effective visualization
- Choose the most appropriate graphs and techniques for your IT data
- Transform complex data into crystal-clear visual representations
- Iterate your graphs to deliver even better insight for taking action
- Assess threats to your network perimeter, as well as threats imposed by insiders
- Use visualization to manage risks and compliance mandates more successfully
- Visually audit both the technical and organizational aspects of information and network security
- Compare and master today¿s most useful tools for security visualization
Contains the live CD Data Analysis and Visualization Linux (DAVIX). DAVIX is a compilation of powerful tools for visualizing networks and assessing their security. DAVIX runs directly from the CD-ROM, without installation.
Errata
Here are a few typos and errors that I have found or others have found in the book. Thanks for reporting them (either via email to me or as a comment here).
- Inside cover: My name is mis-spelled (Rafael instead of Raffael)
- Page 15, Figure 1-7: Similarty should be Similarity in the top right of the figure.
- Page 26: Says 172. It should say 127.
- Page 69, under Chart Axes section: "... the vertical axis is generally the y-axis". This should be the z-axis.
- Page 91, Figure 3-22: Arrow from "web" to "10.0.0.252" should be going the other direction.
- Page 162 at the very top: It should mention that there are four, not three subcategories.
- Page 192: line 13 in example: It should be a tilde ~ instead of the [td].
- Index: MADC should be MACD.
Press / Related Material
- February 2010, Directed musings on computers, music, huskies, ...
- November 2009, Applied Security Visualization Utahcon Blot.
- May 2009, Applied Security Visualization Ethical Hacker Network, JP Bourget.
- March 2009, doing more with less … on the SecurityKitchen.
- March 2009, Slashdot mentioning of the book.
- March 2009, Applied Security Visualization blog post by utahcon.
- February 2009, Better security through better visualization by Michael Kelly.
- February 2009, BOOK EXTRACT: Applied security visualization
- January 2009, Richard Austin reviews Applied Security Visualization for IEEE Cipher
- December 2008, iLogin Book Reviews
- December 2008, Book review on Windows IT Pro
- November 2008, Book review on Slashdot
- November 2008, Raffy's Visualization Book Blog post by Anton Chuvakin
- September 2008, Book Review by Adam Shostack
- September 2008, Q&A: Security Visualization Interview with Mirko Zorz
- August 2008, Book Review by Francois Ropert
- August 2008, Security visualization helps make log files work, Article by Robert Westervelt
- August 2008, Security Wire Weekly: Security Visualization, Interview with Robert Westervelt from TechTarget (podcast)
- August 2008, "Networking data visualization not just for pointy-headed bosses", Interview with Michael Morisy.
- August 2008, Book Extract: Networking data visualisation explained
- August 2008, Interview with Martin McKeay at DefCon 2008 (podcast)
- July 2008, Applied Security Visualization at First 2008 (podcast)
- June 2008, Security Visualization: What You Don't See Can Hurt You
- March 2008 SOURCE Boston Blog about "All the data that's fit to visualize" talk.
- January 2008 Bridging Visualization and Security (video)
- January 2008 Applied Security Visualization (video)
- August 2007 Bar Talk about Security Visualization (podcast)
- May 2007 Applied Security Visualization at First 2007 (podcast)
Past events
- "SecViz 007", BCS 2008, Jakarta, November 2008.
- "SecViz 007", IS Summit 2008, Hong Kong, November 2008.
- "Applied Security Visualization" Workshop, IS Summit 2008, Hong Kong, November 2008.
- IT GRC Visualization, Triangle InfoSeCon, Raleigh, North Carolina, October 2008.
- IT Security Awareness Event at University of MichiganL, October 2008.
- "SecViz 007", BA-Con Argentina, Buenos Aires, September 2008.
- Panel discussion at VizSec, Boston, September 2008
- DAVIX presentation at VizSec, Boston, September 2008
- FIT-IT, Graz, Austria, September 2008
- Workshop on Visualization at DefCon, Las Vegas, August 2008
- "Applied Security Visualization" Workshop, First Conference 2008, Vancouver, June 2008
- "Recent Trends in Security Visualization", RSA Conference, San Francisco, April 2008
- "All the Data That's Fit To Visualize", SOURCE Boston, March 2008
Additional Visualization Tools
Here is a list of visualization tools. This list is a continuation of what you can find in Chapter 9 "Visualization Tools":
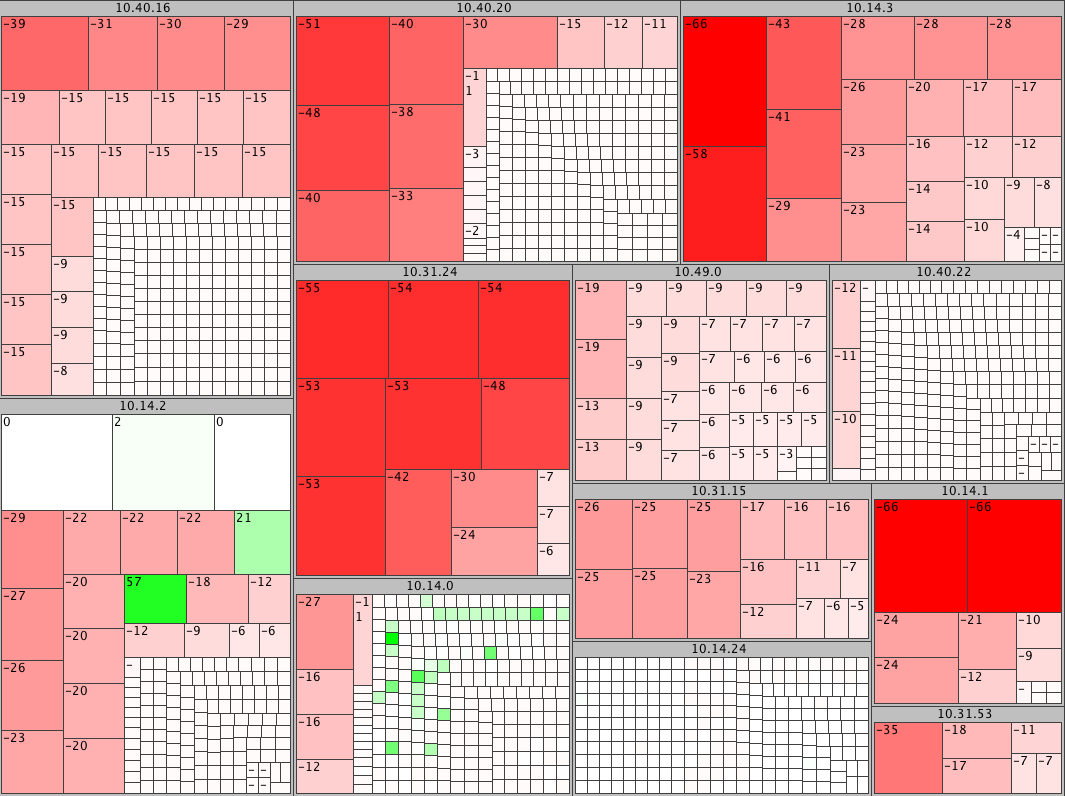
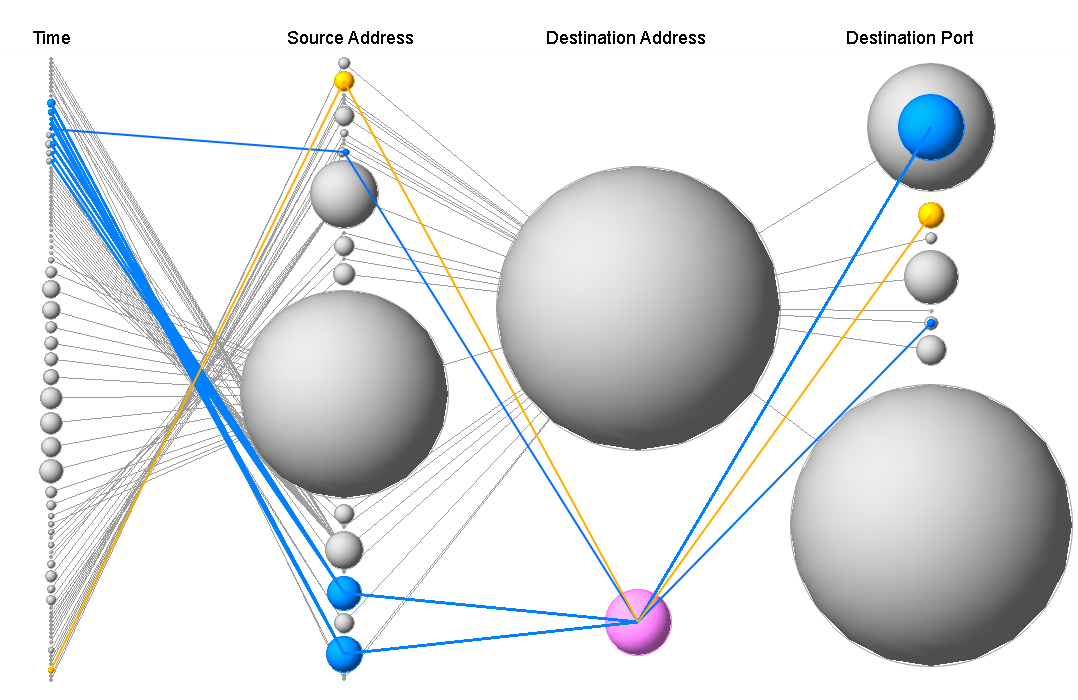
Sample Figures
 |
 |
|
 |
 |
|
 |
 |
|
 |
 |